AI and the Future of Cybersecurity: Opportunities and Risks
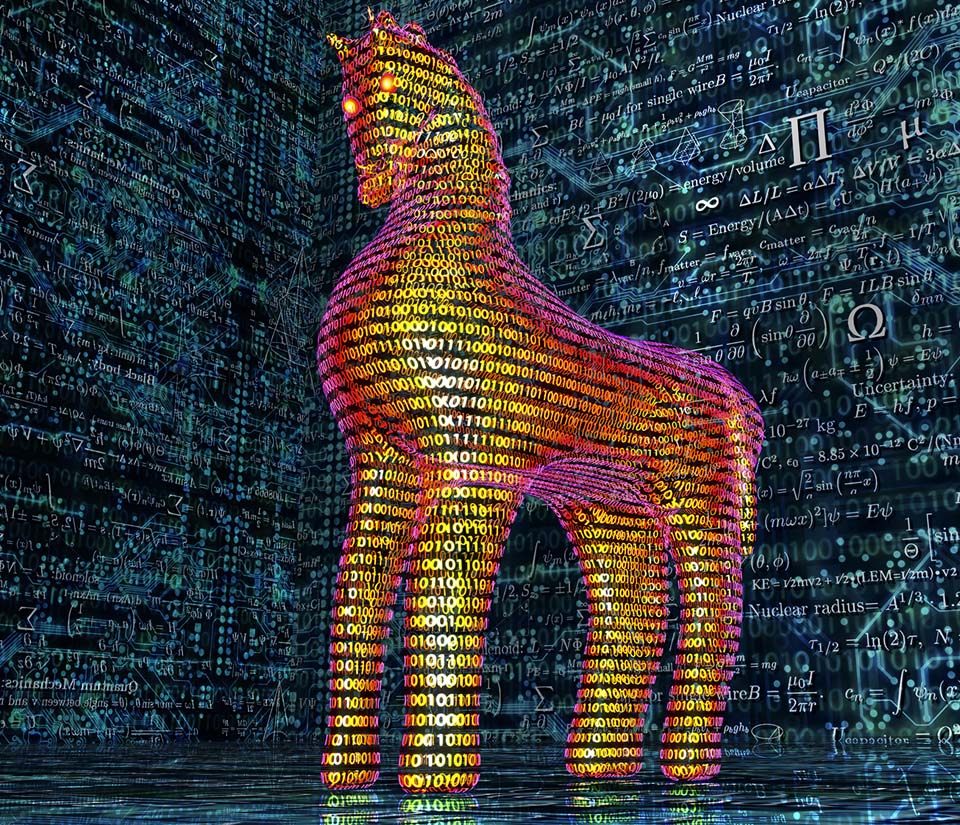
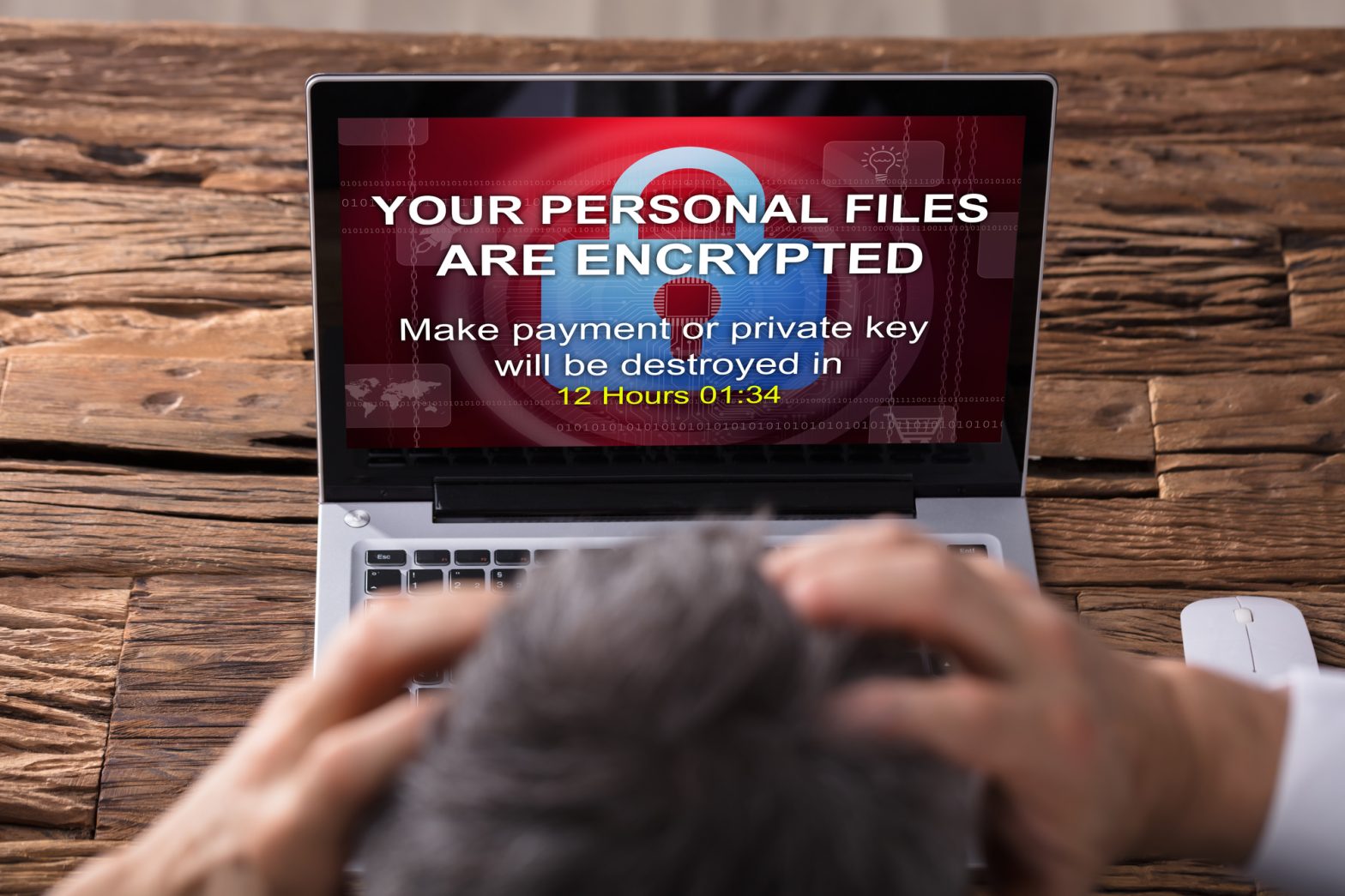
Although once just a staple of science fiction, AI-powered tools are now a pillar of modern security compliance management services. No mere chatbots, these headline features enhance systems’ cybersecurity by detecting threats, predicting vulnerabilities, and responding to incidents in real time. But as this software garners more attention, we must separate the hype from the… Continue reading AI and the Future of Cybersecurity: Opportunities and Risks